NEWS
Cyber Storm to test cyber engineering, computer science students
Cyber Storm 2014 is scheduled to make landfall at Louisiana Tech University on Friday, May 16.
Computer science and cyber engineering students from Louisiana Tech’s College of Engineering and Science will compete against each other and other unknown intruders from academia, industry and government institutions, in a day-long “hackfest” where student teams will engage in a fierce battle in cyberspace to test their skills in network defense and attack strategies. Cyber Storm is designed to raise awareness about the problems our society faces in cyberspace.
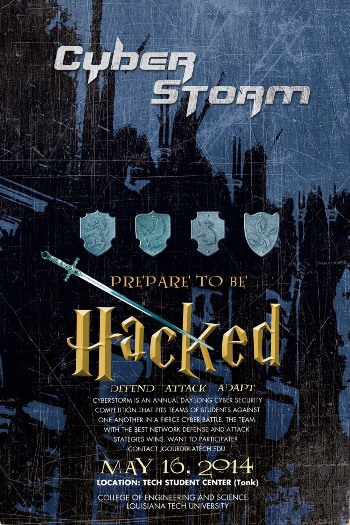 The competition will begin at 9:00 a.m. in the Louisiana Tech Student Center and is open to the public. Members of the campus and local communities are encouraged to attend. Cyber Storm will also serve as the final exam for students in the CSC 442 – Introduction to Cyber Security and CYEN 301 – Computer Network Security classes.
The competition will begin at 9:00 a.m. in the Louisiana Tech Student Center and is open to the public. Members of the campus and local communities are encouraged to attend. Cyber Storm will also serve as the final exam for students in the CSC 442 – Introduction to Cyber Security and CYEN 301 – Computer Network Security classes.
“Most of us consider cyberspace to be the Internet,” said Dr. Jean Gourd, assistant professor and program chair of computer science at Louisiana Tech. “Actually, cyberspace encompasses much more than that. Think of cell phones, buoys in the ocean that monitor wave height and report back to stations, motion sensors in a house that detect intruders and send alerts, and so on. A lot of our infrastructure such as water treatment plants, electric power plants and banking systems utilizes this space as well.
“We use this domain every day and since it involves a large part of most of our lives, it becomes a point of attack.”
Cyber Storm will feature a specially-designed, custom infrastructure to support the competition and team engagement. In addition to hardware and network configuration, event organizers are further designing and implementing a number of critical components that will provide challenges and overall situational awareness during the competition. These include elements such as live scoring and messaging, real-time visualization of the network (including attacks), “King of the Hill” and “Capture the Flag” challenges, cyber security-related challenges, cryptography and steganography challenges, wireless network access challenges and cyber “scavenger hunts.”
“The competitive part of Cyber Storm is only there for fun,” Gourd said. “But it can also serve to show the kinds of fast-paced scenarios that can actually play out in the real world. The students participating do so as their final exam, and they often tell me that they learn more from the event than they do in the entire course. I suppose that this is a good thing as it tries to recreate real-world experiences.”
Cyber Storm spectators are also welcome to join in the competition if they’d like, but all it takes is a glimpse of the work being done by the students to see how complicated things can get in cyberspace.
“We’ve created a unique situational awareness system that attempts to provide a real-time picture of the network throughout the event,” said Gourd. “This is nice as it tries to put a picture to what’s going on in a medium that is not so easy to ‘view’ in the real world.”
Gourd says that, at the minimum, if students and spectators walk away realizing that what they do in cyberspace has the potential to affect others, then he feels he’s been successful.
“The idea of raising computer literacy from simply knowing how to use and interact with computers to knowing how to instruct computers and about the consequences of playing around with them, particularly in cyberspace, is something that I advocate and am passionate about,” explains Gourd. “Just as we must be responsible and aware citizens in society, we must also be responsible and aware citizens in cyberspace.”
Cyber Storm is hosted by the computer science and cyber engineering departments and is sponsored by the Cyber Innovation Center and Computer Sciences Corporation (CSC). For more information, contact Gourd at jgourd@latech.edu or visit http://coes.latech.edu/cyber-engineering/cyberstorm.